LangGraph is an open-source AI agent framework developed by LangChain designed to build, manage, and deploy complex, stateful, and conversational AI agent applications.
LangChain is the easy way to start building completely custom agents and applications powered by LLMs. With under 10 lines of code, you can connect to OpenAI, Anthropic, Google, and more. LangChain provides a pre-built agent architecture and model integrations to help you get started quickly and seamlessly incorporate LLMs into your agents and applications.
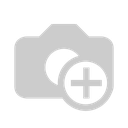
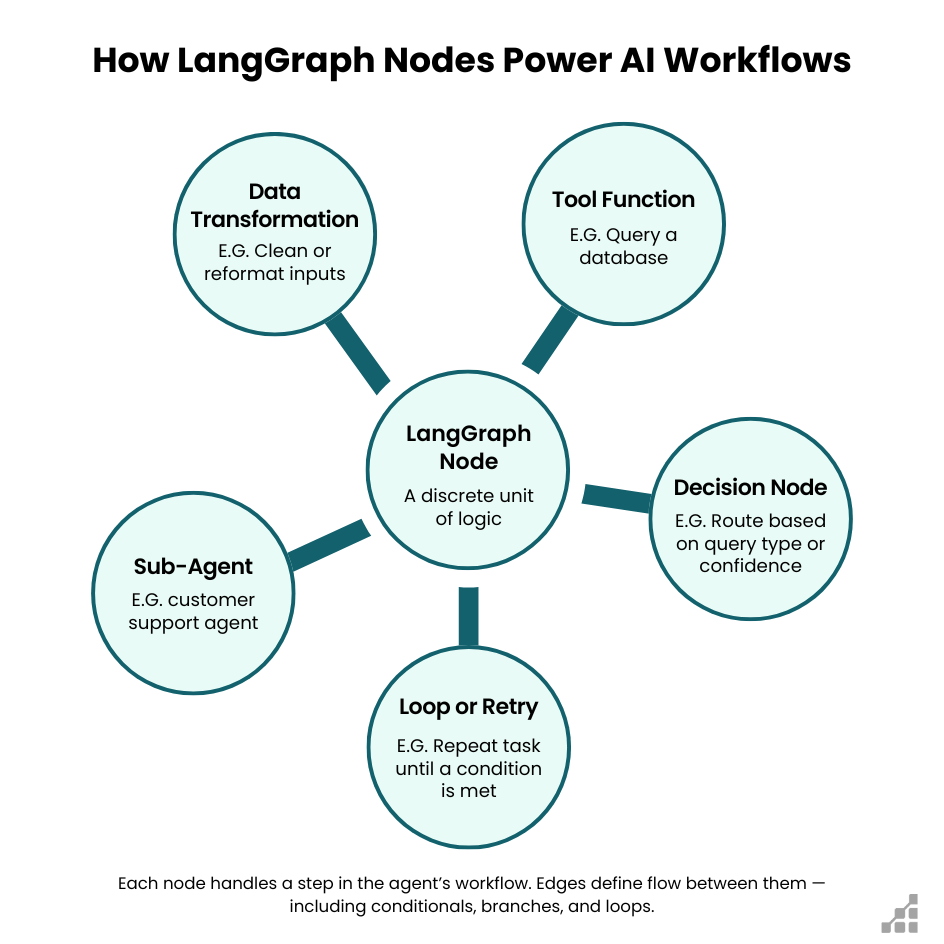
LangGraph is based on graph-based architectures, using key components to define agent behavior.
It extends the capabilities of LangChain by providing a way to structure agent workflows as graphs—consisting of nodes (components/functions) and edges (transitions)—which allows for loops,, complex logic, and persistent state management.
A graph is the orchestrator of our workflow. It combines the three core components — State, Nodes, and Edges — into a structured, executable system.
In LangGraph, which is a library for building stateful, multi-actor applications with LLMs, these components define how the workflow, data, and logic interact.
LangGraph Studio: LangGraph provides LangGraph Studio, a specialized IDE for visualization and debugging of LangGraph applications. This tool offers a visual interface to monitor your agent's execution flow, inspect state changes, and debug complex workflows in real-time, making development and troubleshooting significantly easier.
Building reliable AI agents isn't just about giving them more power. It is about giving them the right structure. With State, Nodes, and Edges as its foundation, and features like Human in the Loop, Memory, and Streaming, LangGraph helps you build agents that don't forget, don't fall apart, and don't leave users frustrated.